The default behavior for an Application Gateway with App Service instance in the backend pool is that the Host header is overridden to match the Web App’s default hostname: *.azurewebsites.net. This is caused by the “Use for App Service” and “Pick host name from backend address” configuration options on the Application Gateway. These requests arrive at the App Service frontend and route to the destination based upon matching Host header.
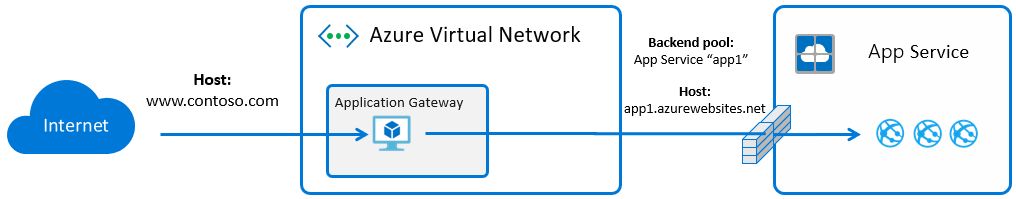
While these settings make initial configuration easier, they do have a few consequences:
- Backend URL exposed when there is a redirect or URL that is built in application logic
- Application behavior issues when the client’s hostname or HTTP protocol do not match what arrives at the backend Web App
- Failed authentication when the auth provider sees the backend Host header, rather than the custom domain accessed by the user
- ARR Affinity is broken to the backend instances, because the Host header is mismatched